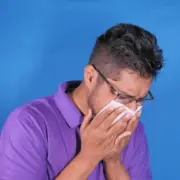
Cyber-Attacks Are Like The Flu
Cyber-attacks are like the flu, even with an injection, eventually, you are going to get ill. It is always there, lurking, waiting to make your life just that little bit harder.
The same can be said of today’s cyber threats. They constantly change, with malware vectors ever increasing.
Many companies are lax, leaving doors open, not deleting user accounts of those who have left, ignoring system alerts, not patching servers and endpoints, have weak email controls, allow fileless attacks or bad URLS.
Some can’t afford the time to investigate an attack so need to be proactive about stopping them. Traditional measures such as anti-virus are no longer good enough to meet the speed of change and are often unable to see new vectors, such as fileless attacks. Proactive systems are required which provide visibility, detection, and prevention, along with automatic\manual remediation.
Technology is available to deal with this and can fit across the whole network, servers to endpoints. It looks at what is normal if anything looks abnormal the process is killed immediately. Any Zero-Day attacks are stopped whereas, traditional forms of detection only kick in once the attack signature is known and implemented, which is far too late.
By using technology to detect a threat, and blocking it, prevents its spread and gives the IT team time to investigate in a quarantined environment. Enabling an exploit to run within a controlled environment, such as honeypots, allows deeper understanding of who the attacker is and their goal. This is useful, especially if the attack was targeted at critical assets, such as intellectual property or finance systems.
Another benefit of using technology is that it generally gives the IT department access to specialist security teams run by the vendor, a virtual in-house security operations team if you like, performing many triage functions and bringing special skills to the fore, which would normally not be available within the organisation.
All businesses need to stay ahead of the game, not to find themselves as the weakest link – goodbye!
The way forward is to use an AI-based system that learns the behaviour of the network. Technologies such as SOAR (Security, Orchestration, Automation, and Response) can link many disparate security technologies together, forming a single platform for management and alert. Being AI-driven, it allows the business to automate some functions, such as address blocking or taking a device offline during an attack.
Another approach is to lock down each endpoint as, in general, these are the most vulnerable to attack. If a protected endpoint starts to perform unusual acts, even if they are valid applications but used in an odd way, the device will be ring-fenced and the IT team alerted of the incident. This happens instantly, minimising the spread of the attack and with the intelligence to know other protected devices within the network, communicating the threat vector so that each endpoint protects itself, even before the exploit runs.
Now is the time to start protecting against the unknowns, as even the security vendors can’t always be on their ‘A game’, but you certainly can.